There seems to be a trend in web security that requires that you type your password, no pasting allowed!
This combined with other password “requirements” are creating problems for people like me that use very secure long passwords. That means I use a password safe that generates long random strings of letters and numbers like:
kUTaVYPuw6KdCLsqhfJ35qHdZcgCqR
BTW, this password is random and not used by me, anywhere!
So when I sign up for a site that does not allow pasting my really secure password, but requires that I type it manually, I end up with passwords like:
Secure4Stupid!
Making my password much less secure. Also most sites use the “onpaste=return false;” trick. This only stops the stupid people, as 5-15 minutes with a Greasemonkey script will defeat that “security” feature. So let’s not think that every idea about password security is a good idea.
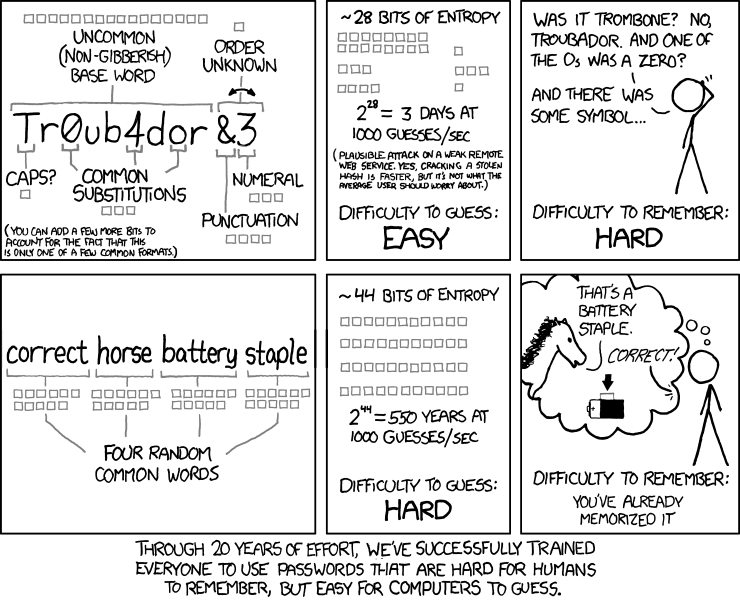
Even the following idea is probably not that secure given that password crackers use dictionaries that contain the words: correct, horse, battery, and staple.
 Another annoyance is sites that do not tell me what the maximum length is for a password on their site. Almost no one tells you this even though they tell you, you must enter at least 8 characters, using letter and numbers…. Since I have had several sites truncate my password, without error or warning, I now have to look at the HTML source code to see if a hint is there.
Another annoyance is sites that do not tell me what the maximum length is for a password on their site. Almost no one tells you this even though they tell you, you must enter at least 8 characters, using letter and numbers…. Since I have had several sites truncate my password, without error or warning, I now have to look at the HTML source code to see if a hint is there.
So here is some password advice for web-site developers and their customers.
- Do tell us the minimum and maximum lengths, characters allowed (numbers, letters, symbols, etc.). Make the maximum something like 255, to allow secure passwords and phrases.
- Do use a hashing algorithm to store passwords for you password protected applications. This also allows for very long passwords, but fixes the hash value length that you need to store to authenticate your users. A really useful function is the Unix crypt() library function that is implemented in numerous languages including C, Perl, PHP, Python, and Ruby.
- Do use standard HTML for accepting passwords for compatibility with more devices.
- Do not disable pasting which causes users to create weaker passwords.
- Do not store passwords in plain text on any system. For clients, use a password safe program to generate and store passwords. For applications and servers, use a strong hashing algorithm to store and compare passwords.
- Do not use JavaScript for security as it is easily circumvented.
- Do not reuse passwords for multiple sites.
For more advice on password security:
